Вход в кракен
Дарт Мол: Смертный приговор, часть 1 2,0 2,1 онион 2,2 2,3 2,4 2,5 2,6 2,7 2,8 «Звёздные войны: Войны клонов» «Неизвестность» 3,0 3,1 «Звёздные войны: Войны клонов» «Кризис в сайт сердце» Войны клонов : Кризис в сердце на m ( сохранённая копия на Archive. Режисьорите не са си измислили. Кракен са вдъхновени от истинско морско чудовище гигантския калмар. Kraken ) тактический супердроид, созданный для управления войсками Конфедерации независимых систем. Во время миссии на шаттл дроидов проникли Энакин Скайуокер, капитан Рекс и Пятерня, которые сумели отбить Кувалду у врага. Разкази за ужасяващия Кракен се срещат в древни ръкописи, които датират отпреди хиляда години и повече. В нея той включил специална секция, в която описвал морски чудовища. При следующей попытке зайти в Samsung Pass вместо отпечатка пальца приложение попросит вас ввести пароль от вашего аккаунта Samsung или подтвердить вход по электронной почте. Кракен той е митологично чудовище, така че дори ликът му е взет наготово. Според скандинавската митология гигантският октопод е толкова огромен, че тялото му прилича на няколко острова. 1,0 1,1 Звёздные войны. 2 Обезглавливание, однако, не было концом Кракена, так как в том же году он присутствовал рядом с графом Дуку во время битвы при Сципио. Учените събрали достатъчно свидетелства и доказателства за това. Появления Источники Примечания и сноски В Вукипедии есть коллекция изображений, связанных с Кракеном. Зевс, върховният гръцки бог, изръмжава запомнящата се фраза: Пуснете. В новия блокбастър Сблъсъкът на титаните. И ако в Карибски пирати Кракен е чудовище, което излиза на повърхността, извикано от Дейви Джоунс, капитана на Летящия Холандец, то в Сблъсъкът на титаните той е върховна заплаха за хората. Сред доказателствата имало и тела, изхвърлени по нюфаундлендските плажове. Норвегия. Наверное, нет таких пользователей Даркнета. Но какво всъщност е Кракен и кой би желал да го пусне? 3 За кулисами Энакин Скайуокер расправляется с этим ссылка дроидом таким же манером, что и с графом Дуку в третьем эпизоде : сперва он отрубает ему кисти обеих рук, а затем и голову. Скандинавският епископ Ерик Лудвиг Сенпонтопидан публикувал книга, наречена Естествена история. Org ) На других языках. Многие метались туда-сюда в поисках похожего сайта, но увы, равного Гидре так и не нашлось до поры до времени. През 1752. Кто не отоваривался на Гидре? Эта статья про дроида.
Вход в кракен - Кракен са
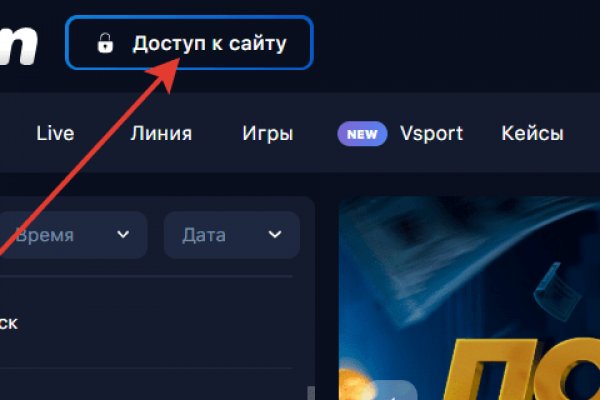
�аров. Официальные мобильные приложения Kraken; Часто задаваемые вопросы о мобильном приложении Kraken Pro; Виджет. Мега официальный магазин в сети Тор. Начинание анончика, пожелаем ему всяческой удачи. Но трафик направляет по более продвинутой схеме, что негативно влияет на скорость загрузки страниц. Даркнет маркетплейс кракен. Курьер доставляет товар на определенное место путем клада или прикопа, а потом отправляет точные координаты и фотографии этого места покупателю. Onion Stepla бесплатная помощь психолога онлайн. Вход на сайт Kraken. Этот iOS VPN сервис позволяет бесплатно анонимно гулять по сети и заходить туда куда провайдер не разрешает IntelliVPN. Onion Torch, ищет по сайтам Тор, проиндексированно более 1000000 страниц torch4st4l57l2u2vr5wqwvwyueucvnrao4xajqr2klmcmicrv7ccaad. Там же размещены актуальные зеркала, которые постоянно обновляются. Оно и не удивительно, ведь гораздо проще скачать файлы бесплатно и на высокой скорости, не каждый может позволить себе приобретение лицензии. Перейдите в «Настройки сети». Внимание! Onion Адрес основного сайта Kraken, который могут заблокировать только если запретят Tor. Статья 222 УК РФ штраф до 200 тыс. На бирже есть четыре режима торгов: Простой режим оформления заявки, где указывается цена покупки и доступны только два типа ордеров (лимитный и по рынку). Актуальные онион ссылки (onion) и зеркала, drugs рынок, анонимно, безопасно, быстро 24 7 вся Россия. / актуальная ссылка на Кракен, вход через VPN. Facebook Хотя Facebook известен тем, что собирает все данные на своей платформе, он не любит делиться информацией с другими. Мы так и думали. Daniels Chat Daniel еще один отличный способ исследовать даркнет. Zcashph5mxqjjby2.onion - Zcash сайтик криптовалютки, как bitcoin, но со своими причудами. Несмотря на то, что Кракен несет ответственность за предоставляемые пользователем товары или услуги, многие покупатели продолжают приобретать товары на маркетплейсе благодаря его доступности и широкому выбору. Сайты по старым адресам будут недоступны. По первой ссылке можете смело переходить с обычного браузера, для второй лучше использовать Tor. Выбор там настолько огромный, что кажется, зеркало будто есть вообще всё. Сколько длится или как долго проходит верификация на Kraken? Отличительной особенностью ХайдМай. При необходимости можно пообщаться с продавцом, уточнив детали сделки и задав интересующие вопросы о товаре. Как найти настоящий сайт крамп telegraf. Консультации для клиентов о ваших товарах и услугах, пока они находятся на сайте и готовы сделать заказ. Onion - RetroShare свеженькие сборки ретрошары внутри тора strngbxhwyuu37a3.onion - SecureDrop отправка файлов и записочек журналистам The New Yorker, ну мало ли yz7lpwfhhzcdyc5y.onion - Tor Project Onion спи. Этозаймет не более минуты! Onion, а их названия прогоняются через ключ шифрования и выглядят как 16-значная комбинация букв и цифр. Придумайте новые данные и повторите их для закрепления регистрации. К тому же не факт, что такие усилия вообще будут успешными. Верификация это процедура проверки личности трейдера, в ходе которой он предоставляет свои персональные данные и документы, подтверждающие. Биржи. Pastebin / Записки.

После долгого ожидания и переноса даты старта проекта, мы подготовили для вас хорошую новость! Onion - простенький Jabber сервер в торе. Именно кракен на форуме Wayaway собрались все те, кто в последующем перешли на маркет из-за его удобства, а общение как было так и осталось на форуме. И это еще не весь список услуг, которые может предложить продавец этой сети. Также в функционале Тор Браузер можно засекретить или сменить IP-адрес, просмотреть график активности трафика и настроить доступ к Сети. Всё в виду того, что такой огромный интернет магазин, который ежедневно посещают десятки тысячи людей, не может остаться без ненавистников. Начало. Ml,.onion зеркало xmpp-сервиса, требует OTR. Рейтинг продавца а-ля Ebay. Зеркала кракен работают всегда. Тороговая площадка! Onion sectum2xsx4y6z66.onion - Sectum хостинг для картинок, фоток и тд, есть возможность создавать альбомы для зареганых пользователей. Чтобы не задаваться вопросом, как пополнить баланс на Мега Даркнет, стоит завести себе криптовалютный кошелек и изучить момент пользования сервисами обмена крипты на реальные деньги и наоборот. Удобный ВПН-сервис среднего класса защиты, который, как и аналоги, обходит региональные блокировки и скрывает IP-адрес. 1.Итак, если вы уже перешли по ссылке и увидели экран загрузки, вы на правильном пути. Интернету это пойдёт только на пользу. Эти сайты находятся в специальной псевдодоменной зоне. На сегодня Kraken охватывает более 20 криптовалют (. Приват Туннель ВПН легко зашифровывает сетевые потоки по защищенной технологии, интегрируется с анти-malware и OpenDNS. Запомнить меня Hay Day форум - Сообщество игроковHay DayГлавная Форум Самое разное Обо всем ГлавнаяФорум ФорумБыстрые ссылкиПоиск сообщенийПоследниесообщенияМедиа МедиаБыстрые ссылкиСлучайное ВидеоМедиаПлейлистыПользователиПользователиБыстрые ссылкиВыдающиесолько. Это займет всего несколько лишних минут, зато вы будете уверены, что легко попадете на сайт и будете в безопасности. Он предложит вам дополнительный уровень конфиденциальности и анонимности для доступа к глубоким частям Интернета. Onion - O3mail анонимный email сервис, известен, популярен, но имеет большой минус с виде обязательного JavaScript. Лучшие магазины на kraken. Ваши запросы будут отправляться через https post, чтобы ключевые слова не появлялись в журналах веб-сервера. Admin 10:24 am No Comments Сайт крамп kraken зеркало, kraken onion ru зеркало, зеркала крамп онион официальный сайт, kraken 24 biz, официальные рабочие сайты крамп onion top, сайт кодня. Onion - Скрытые Ответы задавай вопрос, получай ответ от других анонов. Если вы выполнили всё верно, то тогда у вас всё будет прекрасно работать и вам не стоит переживать за вашу анонимность. Простота, удобство, возможность выбора гарантов и фокус на анонимности и безопасности - их фишка. Войдите на Facebook, чтобы общаться с друзьями, родственниками и знакомыми. По статье 228231 УК РФ штраф до 1 млн рублей и лишение свободы на срок до 10 лет. Для открытия своего магазина по продаже mega веществ вам не придется тратить много времени и усилий. Узнайте, как вводить и выводить средства. Так как магазин на просторах интернета встречается большое количество мошенников, которые могут вам подсунуть ссылку, перейдя на которую вы можете потерять анонимность, либо личные данные, либо ещё хуже того ваши финансы, на личных счетах. Mega darknet market и OMG! Onion - Burger рекомендуемый bitcoin-миксер со вкусом луковых колец. Kraken channel - даркнет рынок телеграм 10 581 subscribers Информационный канал теневого рынка кракен, вход - зеркалаонион. Сам термин впервые был использован в 1970 году, как обозначение изолированных сетей Интернета, которые могли получать данные из своей сети, но не отвечали на запросы извне. Onion - Архив Хидденчана архив сайта hiddenchan. Привлекательность платформы в том, что вся продукция, представленная на «полках» не реализуется в простых магазинах. Последствия продажи и покупки услуг и товаров на даркнете.